Choosing the right security testing tool for your project can be time-consuming. That’s why we’re sharing this vetted list. These First Choice tools cover the most reliable open-source and commercial options across static and dynamic testing, software composition analysis, and infrastructure scanning. Many are free or with generous tiers, and all are easy to boost security in your CI/CD pipeline or run quick on-demand scans.
Security Tools Quiz
Think you know the difference between SAST and DAST? Prove it in our quiz! Not sure yet? Read the article first—then you’ll feel confident about your Application Security Testing knowledge.
Why Automated Application Security Testing Matters
Application Security Testing (AST) is a systematic approach to enhancing applications' ability to defend against security threats. It involves uncovering and resolving security weaknesses within the application's source code.
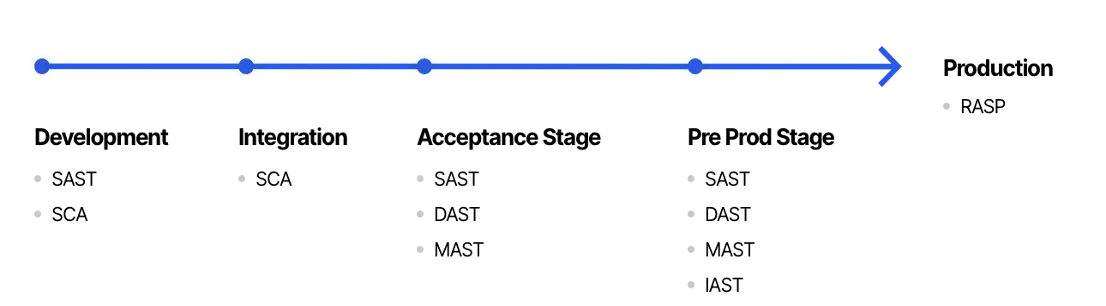
While AST started as a manual process, today’s scale and complexity demand automation. Increased modularity, open-source sprawl, and the growing number of known vulnerabilities and threat vectors require a layered approach. Most organizations combine several application security tools to catch different classes of risks across the application development process:
Common Tool Categories
- Static Application Security Testing (SAST): Analyzes source code or binaries to identify vulnerabilities without executing the program.
- Dynamic Application Security Testing (DAST): Assesses applications in runtime, simulating attacks to discover vulnerabilities from an external perspective.
- Interactive Application Security Testing (IAST): Combines elements of SAST and DAST to identify vulnerabilities during runtime by instrumenting the application.
- Mobile Application Security Testing (MAST): Focuses on assessing security flaws specific to mobile applications and their underlying technologies.
- Software Composition Analysis (SCA): Scans software dependencies to uncover vulnerabilities in third-party components.
- Runtime Application Self-Protection (RASP): Protects applications and their data from security threats at runtime or while the application is actively running.
- Application Security Orchestration and Correlation (ASOC): Streamlines vulnerability testing and remediation through workflow automation.
- Fuzz Testing: Sends unexpected or malformed data inputs to the application and observes its behavior.
- Infrastructure as Code (IaC) Security Scanning: Reviews infrastructure code, such as Terraform, AWS CloudFormation, Ansible scripts, or other declarative configuration files used to provision and manage cloud resources and infrastructure.
- Container Scanning: Tests the security of container images in containerized applications.
First Choice Tools: A Practical Comparison
Our Security Lab recommends considering these tools first when integrating an application security strategy. They have proven effective across many projects. The list compares eight popular SAST, SCA, DAST, and IaC scanning tools by license/pricing, pros, cons, supported languages, and additional notes to help you make an informed decision.
For quick reference, download the comparison table.
Final Thoughts
Security shouldn’t be an afterthought; it should be built into your pipeline from day one. These tools, tested across multiple DataArt projects, offer a strong foundation for securing your application stack. Whether you're working on greenfield apps or legacy modernization, integrating the right mix of scanners into your workflow will catch vulnerabilities earlier and reduce exposure in production.












